TABLE OF CONTENTS
The Blockonomics plugin automatically updates the order status when a Bitcoin payment sent by your customer is confirmed. This works with all our e-commerce plugins. This article explains how to troubleshoot the issue if this is not happening for you.
Problem
If you are using Cloudflare as a proxy or DDoS protection service, it may block callbacks from the Blockonomics server. Follow the steps below to diagnose and resolve the issue.
Please check if any of the following apply to you:
- You are using localhost or an unreachable test server:
We cannot send callbacks to your localhost server. This is expected behavior and is OK. - You are getting an SSLError in Test Bench > Callback Logs:
If your site does not have an SSL certificate, change the callback URL to start with http:// .
If your site is SSL enabled, check the validity of your SSL certificate. We do not support self-signed certificates. If your site appears SSL validated in the browser, make sure intermediate certificates are not missing (because we usecurlfor callbacks).
You can diagnose by testing your site on https://www.ssllabs.com/ssltest/ - You have DDOS protection:
You need to identify the DDoS protection mechanism and follow the steps mentioned below.
Diagnosis
To confirm the issue please check Test Bench > Callback Logs.
If the Callback Status is green "200" (as shown in the image below), then everything is working correctly.

If the Callback Status appears in red (number at the end), then you are experiencing this issue and we cannot send callbacks to your server.
First confirm that Cloudflare is blocking the callback request.
Log in to your Cloudflare Dashboard.
Navigate to Security > Analytics > Events.
Look for requests originating from the following IPs:
44.241.250.59 (BTC / USDT callback server)
44.225.81.126 (BCH callback server)- If you see these IPs being Blocked, Challenged, or Managed, then CloudFlare is preventing the callback from reaching your server.
If you see such events, continue with the steps below to whitelist the callback server.

Cloudflare
Add Security Rule
Please follow the steps below to add a Security (Custom WAF) rule.
- In CloudFlare Dashboard, go to "Security" > "Security rules" and click on "+ Create rule" > "Custom Rules" button to create a new rule.
- Enter a memorable Rule name like "Blockonomics".
- Click the dropdown below "Field" and select "IP Source Address".
In the dropdown below "Operator", make sure the value is set to "equals".
In the "Value" field, add the IP you want to whitelist. - To add more IPs, add more rows by clicking on "Or" button at the end of row.
- Add following IPs (as shown in image in Step 6):
- 44.241.250.59: BTC/USDT callback server
- 44.225.81.126: BCH callback server (If you are using BCH payment method)
- Make sure the "Action" is set to "Skip", "Log matching requests" is enabled, and all rules are checked to be skipped.
- Once you have made the changes as shown in the image below, click "Deploy"at the end of the screen.
- You should now see this new Security Rule added and Active under Security → Security Rules as show below:
Add Cache Rule
Please follow the steps mentioned below to add Cache rule:
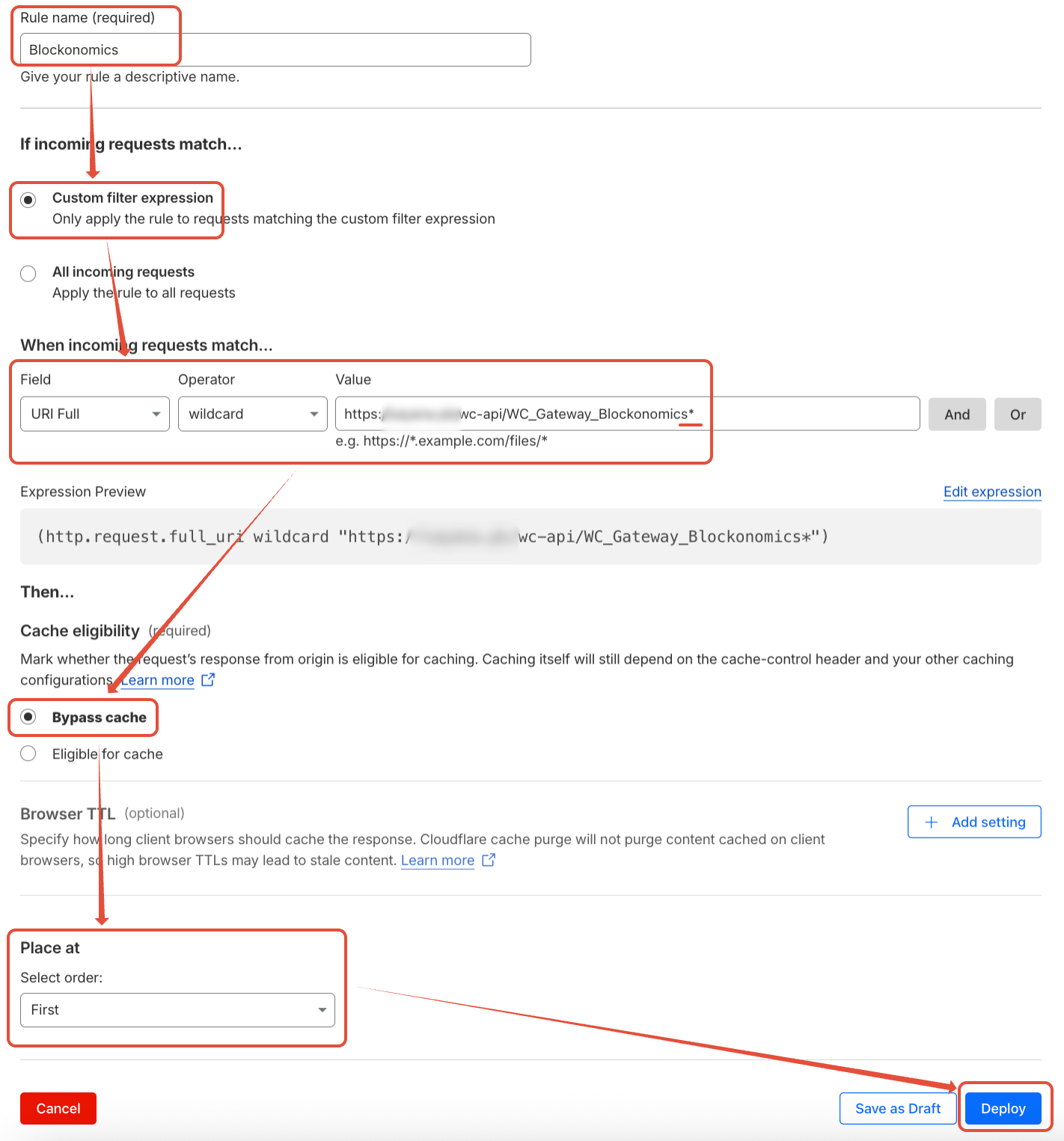
- In CloudFlare Dashboard, go to "Caching" > "Cache Rules" and click on "+ Create rule" button to create a new rule.
- In Rule name add something like "Blockonomics".
- Under "If incoming requests match..." select "Custom filter expression" and following values:
- Field: "URI Full"
- Operator: "wildcard"
- Value: Add Callback URL for your store with path after "?secret" remove and '*' at the end
- e.g: for WordPress store, if your callback URL is https://example.com/wc-api/WC_Gateway_Blockonomics/?secret=abc123, add Value like: https://example.com/wc-api/WC_Gateway_Blockonomics*
- e.g: for WHMCS store, if your callback URL is https://example.com/modules/gateways/callback/blockonomics.php?secret=abc123, add URL like: https://example.com/modules/gateways/callback/blockonomics.php*
- Under "Cache eligibility" select "Bypass cache".
- Under "Place at > Select order:" select "First".
- Once you have made all the mentioned changes as shown below, click on "Deploy"
- Now in "Caching > Cache Rules", you should have a Cache Rule added and Enabled like shown below:
Still not working?
If the WAF rule does not resolve the issue, temporarily disable bot fight mode to test whether it is interfering with the callback.
If callbacks begin working after disabling it, the WAF rule likely needs adjustment to correctly skip Bot Fight Mode for our IPs.
If callbacks still fail, please share a screenshot of Security > Analytics > Events from your Cloudflare dashboard filtered by our IP address(s).

WordFence/Others
If you are using any other DDOS protection mechanism you can whitelist the IP of our callback server:
44.241.250.59 – BTC / USDT callback server
44.225.81.126 – BCH callback server
End Note
- After bypassing the DDOS protection, try to generate multiple test callbacks (Using Test Bench > Callback Logs) within a minute / less period and and confirm that you receive 200 status responses.
- If you are using a custom or programmed API endpoint, make sure the callback endpoint returns a clean HTTP 200 response with no errors.